Are your Apps Secure? An End to End Guide for Mobile Application Security
Mobile Application Security
When we were an agrarian nation, all cars were trucks, because that’s what you needed on the farm. But as vehicles started to be used in the urban centers, cars got more popular … PCs are going to be like trucks. Less people are gonna need them and this is going to make some people uneasy. –Steve Jobs
The above lines depict that the lives of people rely much more on mobile applications than web applications moving ahead.
As people are habituated in using mobile for all the daily activities right from checking mails, instant messaging, buying and selling things online using augmented reality and doing financial transactions. Through these businesses can gather PII(Personally identifiable information) such as the location, usage statistics, phone number, comments and other meaningful metrics about users, which can help them make precise decisions to improve their services. “Care to be aware!” Not only they are one click away from getting things done to you but harmful when data gets into the wrong hands.
Thus, the need for mobile application security is unavoidable.
What is Mobile application Security?
Mobile Application Security can be defined as software security of mobile applications that run on various platforms like Android, iOS, iPad OS and Windows phone. It is a preventive measure from malicious threats and other digital frauds that risk personal and financial data breach.
Mobile Application Security Testing involves effective security testing by understanding the business purpose of the application , the type of data it deals with and foresee the ways in which a malicious user would try to attack it.
Building blocks of Mobile Applications
The coding languages used to develop mobile applications are of 2 types.
Native App development : The code base involved is platform specific and executes only on 1 particular platform.
- Ex: Java , Kotlin , C/C++ , Objective C , Swift
Hybrid App development: The code base involved executes on various platforms.
- Ex: Cordova, React-Native, Flutter and many more.
Types of Mobile Application Security Testing
Static Testing:
- Deals with source/ binary code
- Will not involve any configuration
- Less accurate
- Can notice bad practices made by the developer
- Easily identifiable issues: Code quality, Build Configuration, Cryptography(at times) , Platform issues
Dynamic Testing:
- Deals testing application on emulators/real devices.
- Involves configuration to get results by working on the app
- More accurate
- Can notice real world scenarios by being an end user.
- Easily identifiable issues: Network testing , Forensic testing , Cryptography(at times)
- Both are equally important in order to make applications secure.
Executive Summary:
- 85% of Mobile Apps have Security Vulnerabilities.
- 49% of Mobile Apps Leak Personal Data to Violate GDPR.
- 73% of Android Apps Leak Sensitive Data to System logs.
- 18% of iOS Apps Leak Sensitive Data to System Logs.
- 1 in 5 android apps use insecure HTTP instead of HTTPS.
- 1 in 7 iOS apps use insecure HTTP instead of HTTPS.
Impact due to weak application security:
- Users phone numbers, location, login credentials to any device or email, social networking, banking websites being stolen.
- Gaining credit and debit card numbers and reselling it
- Taking over access to users business networks
- Illegal creation of app clones by stealing the code base or by stealing intellectual property of company who owns the app(Identity theft)
- Making possible in using access premium features especially in game apps for free impacting the revenue of app owner
Vulnerabilities in Mobile applications
Mobile applications focus on a smooth interface and in providing the best features to users. Basically it will not be potential enough to serve as anti-virus and to securely transmit/receive data over the internet.
Most of the common vulnerabilities are documented by experts of Open Web Application Security Project(OWASP) for reference of developers popularly known as OWASP Mobile Top 10.This list acts as a guide for developers in building secure applications and incorporates best coding practices.
Enlisted below are the “OWASP Mobile Top 10” which was last updated in 2016.
- Improper Platform Usage
- Insecure Data Storage
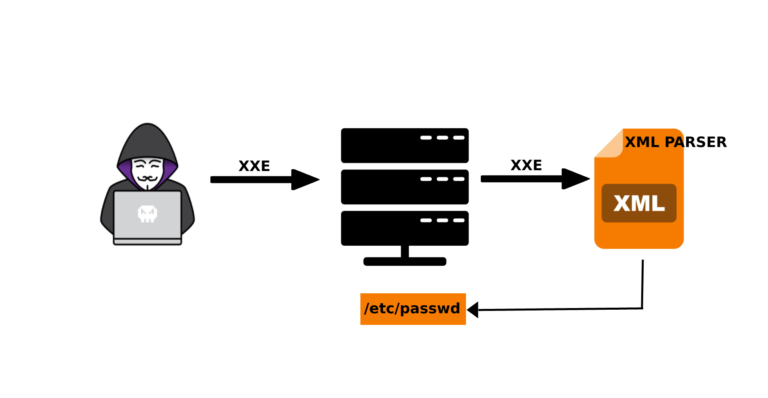
- Insecure Communication
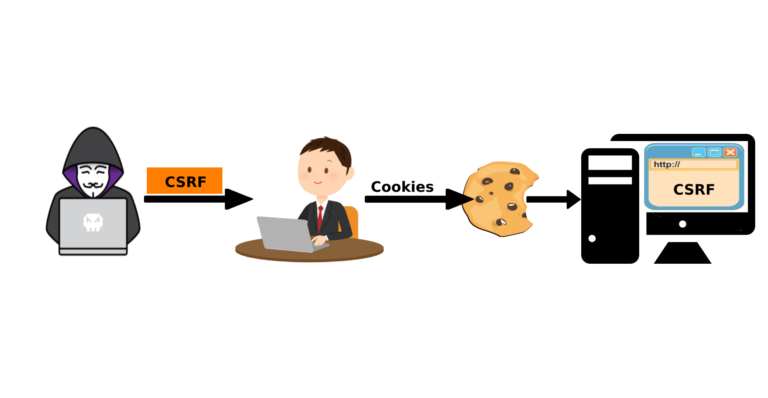
- Insecure Authentication
- Insufficient Cryptography
- Insecure Authorization
- Client Code Quality
- Code Tampering
- Reverse Engineering
- Extraneous Functionality
Mitigation Strategies to secure mobile applications
- Enhance Data Protection: Include well implemented data encryption while the data is transferred between devices , use firewalls whenever necessary. Establish specific security strategy and policy that actively compile and resolve all the possible data breaches.
- Force Session Logout: Never let a user’s session to remain active after they’ve logged out or closed your app. Apps must be enforced with the end of session of a user after a certain amount of time or after every logout to increase security.
- Actively monitor Rogue apps: Fraud watch on both legitimate and unauthorized app download platforms for any apps that carry your brand name and logo.
- Apply multi factor authentication: It’s just one step ahead in making sure the authorization is secure by covering up for weak passwords which can be easily guessed by hackers and compromise the security. This can be sent through SMS, email, Google Authenticator, or biometric methods.
- Penetration Testing: In order to prevent application from hackers, think like a hacker. This process involves recreating activities like a hacker and find the weakness of application. It is required to perform regularly in order to keep the application secure.
- Ensure HTTPS Communication: It offers secure data transmission over a network. The communication protocol is encrypted by TLS(Transport Layer Security)which ensures data privacy over various channels.
- Restrict User Privileges: Be discreet in declaring permissions required for application. Even though the permission to application makes it more freedom and power to work more effectively, at the same time makes it more vulnerable to users. So, No application should seek permission beyond its functional area.
- Prevent Usage of Personal Devices: Never use personal laptops/desktops for the app development. Malware and Trojans travel from one device to another in this manner. Avoid saving passwords. This might open the network to a ton of infections that may have been gathered on an employee’s device. Each device in an office network has to be scanned thoroughly with firewalls and antivirus.
With this, I conclude that the businesses should consider the impact of mobile application security and impact on brands over all.Do not rush development or patches. Keep monitoring for malwares. As online fraud is constantly evolving, users prefer apps which are secure rather than apps which seize their data. Hence, Developers need to strive in creating applications which focus on security and satisfy the needs of users as well.

Harshitha P
Malware Analyst & Author at Security Souls